🔍 Encryption কী?
Encryption হচ্ছে এমন একটি প্রক্রিয়া যার মাধ্যমে কোনো তথ্য বা ডেটা কোডে রূপান্তর করা হয় যাতে এটি অপরিচিত বা অননুমোদিত ব্যক্তির জন্য বোধগম্য না হয়। এটি মূলত তথ্য নিরাপত্তার একটি গুরুত্বপূর্ণ উপাদান।
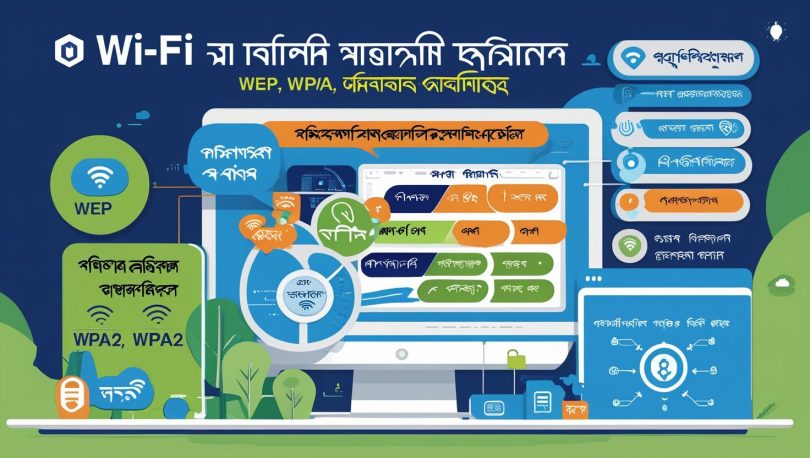
📡 Wi-Fi Encryption কী?
Wi-Fi Encryption হলো একটি প্রক্রিয়া যার মাধ্যমে Wireless Router এবং আপনার ডিভাইস (যেমন: পিসি বা মোবাইল) এর মধ্যে ডেটা এনক্রিপ্টেড ফর্মে আদান-প্রদান হয়। এর ফলে তৃতীয় পক্ষ সহজে আপনার নেটওয়ার্কে অনুপ্রবেশ করতে পারে না।
⚠️ মনে রাখবেন, সব Wi-Fi নেটওয়ার্ক এনক্রিপ্টেড হয় না। অ-এনক্রিপ্টেড নেটওয়ার্কগুলো খুব সহজেই হ্যাক হওয়ার ঝুঁকিতে থাকে।
🔐 Wi-Fi Security Protocols এর বিবর্তন
১৯৯০ সালের পর থেকে বিভিন্ন Wi-Fi সিকিউরিটি প্রোটোকল বাজারে আসে। সবচেয়ে উল্লেখযোগ্য তিনটি হল:
- WEP (Wired Equivalent Privacy)
- WPA (Wi-Fi Protected Access)
- WPA2 (Wi-Fi Protected Access II)
চলুন এগুলো নিয়ে বিস্তারিত জেনে নিই।
🧷 WEP (Wired Equivalent Privacy)
প্রবর্তন: সেপ্টেম্বর ১৯৯৯
Key Size: প্রথমে ৬৪-বিট, পরে ১২৮-বিট
দুর্বলতা: Key সাইজ ছোট হওয়ায় সহজেই হ্যাক করা যেত
স্ট্যাটাস: ২০০৪ সালে বন্ধ ঘোষণা
🔴 সফটওয়্যার দিয়ে মিনিটের মধ্যে এই সিকিউরিটি ভেঙে ফেলা যেত।
🔐 WPA (Wi-Fi Protected Access)
প্রবর্তন: ২০০৩ সাল
Key Size: ২৫৬-বিট PSK (Pre-Shared Key)
Encryption Method: TKIP (Temporal Key Integrity Protocol)
উন্নতি: WEP থেকে অনেক বেশি সিকিউরড
দুর্বলতা: পরবর্তীতে এই প্রোটোকলও হ্যাকযোগ্য হয়ে পড়ে
🔒 WPA2 (Wi-Fi Protected Access II)
প্রবর্তন: ২০০৬ সাল
Encryption Method: AES (Advanced Encryption Standard)
সুবিধা: শক্তিশালী এনক্রিপশন এবং নিরাপত্তা
PSK ব্যবহার: হ্যাঁ
দুর্বলতা: কিছু অ্যাপ brute-force করে key ধরার চেষ্টা করে
🟢 এখনো অধিকাংশ আধুনিক রাউটার WPA2 ব্যবহার করে।
🛡️ উপসংহার
Wi-Fi Encryption আপনার নেটওয়ার্কের প্রথম সুরক্ষা স্তর। আপনি যদি Wi-Fi ব্যবহার করেন, তবে অবশ্যই WPA2 (বা তার পরবর্তী সংস্করণ যেমন WPA3) এনক্রিপশন সক্রিয় করে রাখুন।
📌 গুরুত্বপূর্ণ টিপস:
- Public Wi-Fi ব্যবহারে সতর্ক থাকুন
- রাউটারের Default Password পরিবর্তন করুন
- সর্বশেষ Firmware আপডেট নিশ্চিত করুন
✅ SEO Keywords Used:
- Wi-Fi Encryption কি
- WEP, WPA, WPA2 বাংলা
- Wi-Fi সিকিউরিটি প্রোটোকল
- Wi-Fi হ্যাক থেকে বাঁচার উপায়

If you’d like me to proceed with any of these, please just let me know from the site techtweet.xyz! Also if you need to learn something new than subscribe YouTube : ASP.NET With SQL SERVER